Our data center network administrators have recently been solving problems our customers who are unable to connect to the remote desktop of their server via TCP port 3389. Analysis of their network traffic is following after each client report and in all cases an abnormal number of connections to a source from the Russian Federation has been detected. Unfortunately, this is not a joke, but a fact.
You may know this from your own experience. You want to connect to the remote desktop of your server, but for some reason you can’t. Your colleague is connected and other server services are working properly. So you start looking around. You check your router, you contact your ISP. And suddenly everything works again. You close the matter, claiming it was a “flare-up”, and get on with your work. However, this problem repeats itself more and more often, and the moment when your accountant can’t connect to the server to process the VAT, the desperation takes on a whole new dimension.
The cause of the above mentioned behavior may be an excessive number of connections to the Remote Desktop Server (RDS) port. The service is overwhelmed by the excessive number of connections and either stops responding or simply does not get to the server in time for your connection request. This is typical behavior of a DoS/DDoS attack.
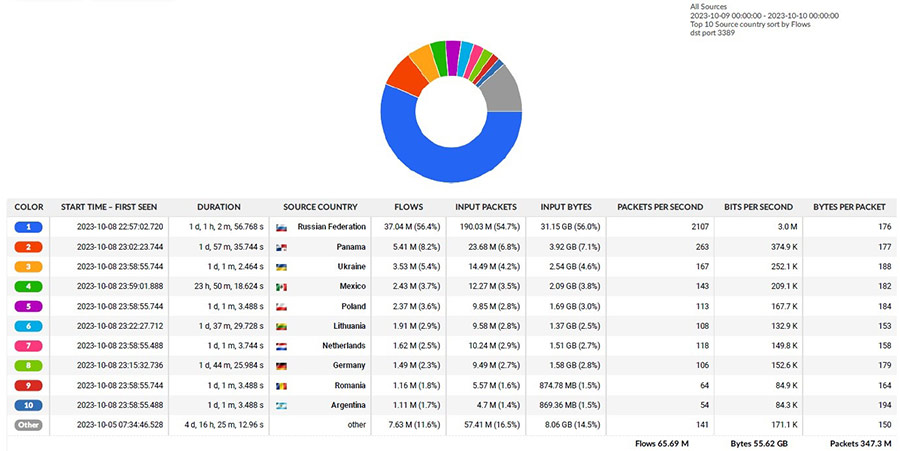
Data flow analysis
Network administrators have been analyzed an hourly sample of Coolhousing data center traffic and the result is quite alarming. The number of connections to TCP port 3389 is sovereignly led by traffic sources originating from the Russian Federation, with a share of 56.4%. The second place was taken by sources from Panama with 8.2% and the third place belongs to Ukraine with 5.4%.
It is possible to speculate whether the significantly higher number of connections from the Russian Federation is related to the ongoing conflict in Ukraine, but from the point of view of security and availability of network services this fact needs to be solved. But how?

The solution is a VPN
We have been providing virtual private network, or VPN, services in our data centre for many years and we know that from a security perspective, it is a highly functional and affordable solution. But it depends on which route you want to take.
1) Without worry – Coolhousing SSTP VPN
The easiest and fastest solution without worries are the so-called server management services such as remote desktop, SSH or IPMI, iLO, iDRAC and others that are hidden from the public behind VPN. A fully out of band SSTP VPN service is just such a solution. For physical servers, the service is provided on a physically dedicated network interface and for virtual servers through a second virtual LAN.
2) Comprehensive solution – private VPN with Firewall
Another option is a dedicated pre-configured physical box that will perform firewall services with automatic blacklisting. Only the ports or services you want will be allowed through the firewall, and if these ports are overused, the attacker is blacklisted and his connections are automatically dropped. This step both saving performance and increasing security. In addition to such an automated firewall, an SSTP or L2TP VPN is set up purely for your use. Our administrators will tailor such a solution and hand it over to your management.
3) Complete managed solution – managed VPN with Firewall
If you’re interested in a private VPN solution with a firewall, but you are not sure if you can handle the subsequent management, there is an option for you with management from us. Again, this is a dedicated physical or virtual box just for you, on which firewall rules are tailored to the project and the VPN is included. In addition you will receive monitoring and supervision services by our L2 network administrators who are ready to solve any incidents 24/7. And you don’t have to worry about a issue.
As you can see, there are several solutions. You just have to choose according to your skills and possibilities. Put yourself in the hands of professionals who really care about the security of your servers and network.
Coolhousing team